The NSD Certified Threat Hunter, 52 hours program is a job oriented industry certification. The focus is on:
Unlock Lifetime Access to ISAC Certifications with Complimentary Training and Free of cost Online Internship: pay only for certification and lab costs.
Our advanced technical training program is available on demand for groups of at least 10 participants. For further details, please contact us.
Learn everything to get started Forensics Investigations.
Use critical thinking to assess normal behavior patterns, identifying unusual network activities and potential security threats.
Understand hunting procedures, the Cyber Kill Chain, and MITRE’s ATT&CK Framework to proactively track and address threats.
Work with threat intelligence and correlation tools to connect data points and gain insights into potential security risks.
Leverage SOAR and data analysis tools to handle extensive data volumes efficiently, enhancing threat detection and response.
The course is best suited for:
Get 60 days access to course videos on the e-learning portal.
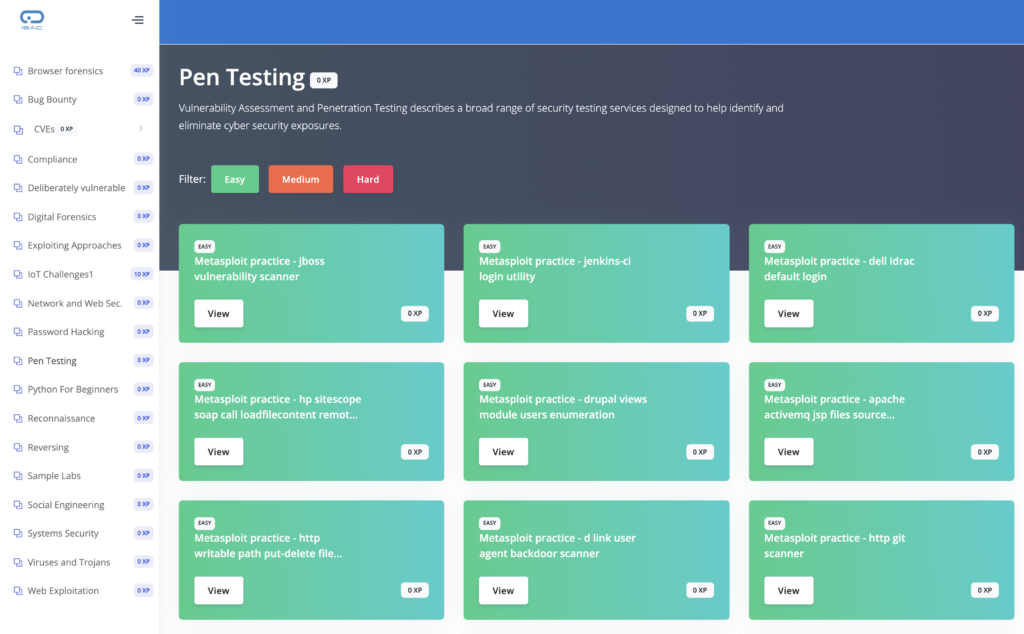
60 Day access to Cyberange Virtual Labs (ID/Password will be sent via email)
Get listed in the National Security Database program at the Falcon level by completing the program.
The Examination includes two free attempts, allowing candidates a second chance to improve their scores or deepen their understanding without additional costs. This benefit supports candidates in achieving certification with confidence and flexibility.
© 2021 All rights reserved | Support Phone: +91 8882-560-560 | SUPPORT@ISACFOUNDATION.ORG