The SOC Analyst program is an 85-hour, job-oriented industry certification designed to equip participants with essential skills for a career in cybersecurity. The program focuses on triaging and root cause analysis (RCA), effective threat hunting approaches, and leveraging threat intelligence for detecting attacks.
Unlock Lifetime Access to ISAC Certifications with Complimentary Training and Free of cost Online Internship: pay only for certification and lab costs.
Our advanced technical training program is available on demand for groups of at least 10 participants. For further details, please contact us.
Open Source Intelligence is the lucrative ocean of information, that everyone wants to dive in. Join the program and enhance your skills.
It also covers Security Orchestration, Automation, and Response (SOAR), User and Entity Behavior Analytics (UEBA), and provides practical training in event log analysis.
Continuously monitor networks for security threats, investigating breaches and incidents to ensure timely responses.
Utilize security tools such as firewalls and encryption software to safeguard systems, documenting and assessing breaches when they occur.
Collaborate with the security team to test network defenses, identify vulnerabilities, and implement fixes to maintain high-security standards.
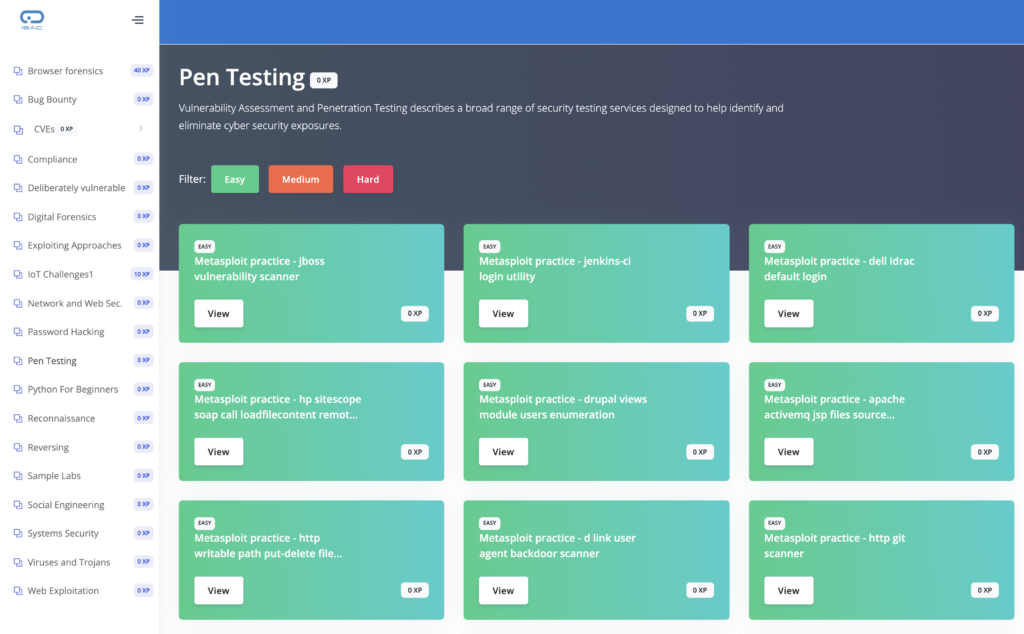
Develop IT security best practices, perform penetration testing, and stay informed on the latest security trends to guide strategic improvements.
The course is best suited for:
Get 60 days access to course videos on the e-learning portal.
60 Day access to Cyberange Virtual Labs (ID/Password will be sent via email)
Get listed in the National Security Database program at the Falcon level by completing the program.
The Examination includes two free attempts, allowing candidates a second chance to improve their scores or deepen their understanding without additional costs. This benefit supports candidates in achieving certification with confidence and flexibility.
© 2021 All rights reserved | Support Phone: +91 8882-560-560 | SUPPORT@ISACFOUNDATION.ORG