The NCBBR, a 64-hour program offered by ISAC, is a unique opportunity for both experienced and novice cybersecurity enthusiasts to receive training, earn rewards, and gain recognition for reporting bugs—especially those involving security exploits and vulnerabilities—legally and ethically.
Learn everything to get started with Bug Bounty programs. Participate with confidence in hackathons and various cybersecurity competitions!
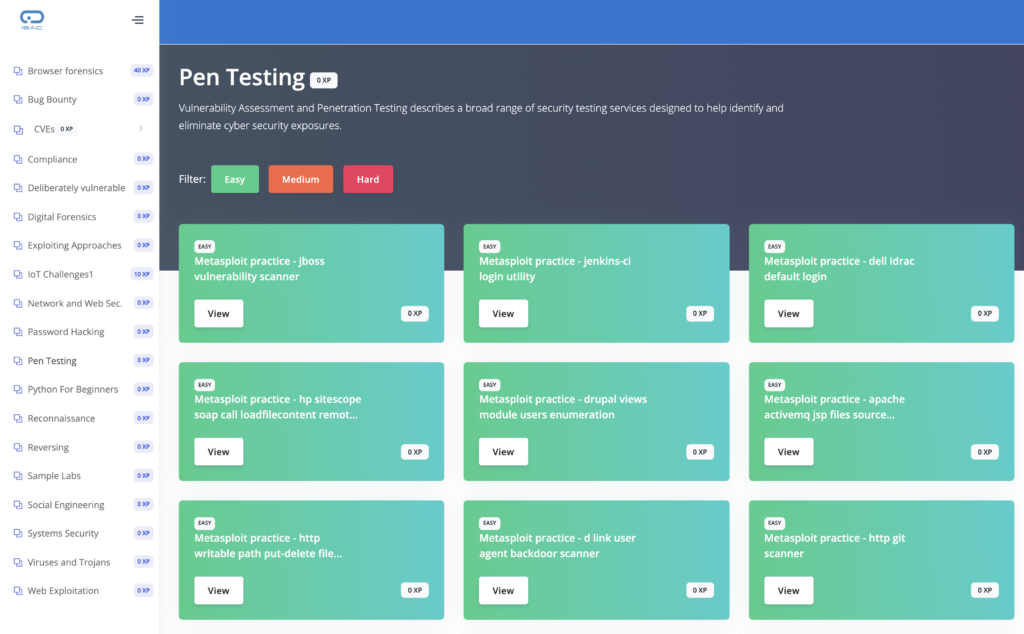
The Program allows you to quickly start your career in this challenging, adventurous and rewarding field with hands-on training and virtual labs.
The NSD Certified Bug Bounty Researcher allows you to quickly get started with hunting bugs and earning rewards from various bug bounty programs.
Register with confidence in various hackathons and hacking competitions after doing this course
Mastering the program will set you in the right direction with potential recruiters. Get jobs in cyber security faster with experience in bug bounty hunting.
The course is best suited for:
 Get exclusive scripts to speed up your bug bounty process, monthly CVE guides, and connect with top experts for insights.
Get exclusive scripts to speed up your bug bounty process, monthly CVE guides, and connect with top experts for insights.
 Win monthly cash prizes of INR 10,000+ and earn weekly rewards by submitting disclosures on the BreachPoint platform!
Win monthly cash prizes of INR 10,000+ and earn weekly rewards by submitting disclosures on the BreachPoint platform!
© 2021 All rights reserved | Support Phone: +91 8882-560-560 | SUPPORT@ISACFOUNDATION.ORG